Featured

Gregor Mitscha-Baude
June 05, 2026
11 min read
formal-verification
zk
circuits
tools
Clean, our circuit DSL, is growing toward verification of complex multi-AIR ensembles. We introduce channels as a way to model lookups, permutation arguments, and zkVM cross-table interactions, then explain how local gadget proofs can compose into global soundness theorems. Watch our talk from ZKProof 8 or read the post.
Read →

ZK/SEC
May 25, 2026
1 min read
educative
security
MPC
mpcsec.org is a new collaborative reference for common pitfalls in MPC implementations and the cryptographic primitives they rely on, built with contributors from zkSecurity, Trail of Bits, Partisia, and Zama. If you build, audit, or deploy threshold signatures, distributed key generation, or other MPC protocols, it's a starting point for the mistakes you don't want to repeat.
Read →
ZK/SEC
June 06, 2026
1 min read
announcement
zkNews is now open to everyone. When we first launched, access was limited to a small beta group to keep things stable while we found our footing. That rate limit is gone. Anyone can now sign up, submit links, and join the discussion at news.zksecurity.xyz. Come help us build the home for zero-knowledge news.
Read →
Marco Besier
May 18, 2026
8 min read
sum-check
algebraic reductions of knowledge
tensors
linear maps
This post is all about the maps that let us move between modules without breaking their structure. We’ll see when a map is truly “linear,” when two modules are (secretly) the same, and why two-input maps deserve special attention. Along the way, (bi-)linear maps and isomorphisms become less like abstract definitions and more like tools we can actually use. By the end, we’ll have all the tooling we need to tackle abstract tensor products head-on.
Read →
Marco Besier
May 10, 2026
9 min read
sum-check
algebraic reductions of knowledge
tensors
rings
modules
In this part of our series, we start introducing the algebraic language needed to formalize sum-check as a tensor reduction. We start with the basics of rings and modules. Rings generalize fields by dropping the requirement that every non-zero element has a multiplicative inverse. Modules then generalize vector spaces by allowing scalars to come from a ring instead of a field. In this post, we’ll use plenty of examples to make these ideas concrete and build intuition along the way.
Read →
Minsun Kim
May 09, 2026
5 min read
security
zk
zkvm
We found a critical soundness bug in Jolt’s transparent verifier that allowed a forged proof for an invalid execution to verify. The issue was fixed quickly after disclosure, and the full PoC and write-up are available in the linked repository.
Read →
Mathias Hall-Andersen
May 08, 2026
3 min read
educative
zk
elliptic-curves
monero
Notes and proofs for the divisor-based ECIP protocol of Eagen, written with Diego F. Aranha and supported by MAGIC Grants. The document is self-contained: it works through the necessary algebraic geometry, the interactive proof and its soundness, the composition with a simulation-extractable NIZK, and the R1CS verifier circuit used by Parker's gadget in Monero's FCMP++.
Read →
Suneal Gong
May 07, 2026
10 min read
encrypted mempool
blockchain
MEV
threshold encryption
Encrypted mempools are an emerging approach to reducing transaction-ordering MEV. They are not just normal mempools with encryption added on top: they introduce a new security boundary around the exact moment a transaction becomes plaintext. This post explains the security model, the core invariant, and the subtle failure modes protocol designers need to consider.
Read →

ZK/SEC
May 06, 2026
4 min read
announcement
zk
security
event
On May 7th, we'll be in Rome sponsoring zkSummit14. A look back at a decade of progress in zero-knowledge, the current state of ZK security based on 100+ audits, and why events like zkSummit have become infrastructure for the field.
Read →
Mathias Hall-Andersen
May 05, 2026
8 min read
cryptography
algebra
soundness
zk
A one-character repeated-squaring bug in Inferno's Limbo implementation turns the intended random polynomial check into a linearized Frobenius check over a binary extension field. This post walks through why the usual Schwartz-Zippel argument disappears, how periodicity of the Frobenius map makes collisions immediate after 64 multiplication gates, and how even smaller circuits can cheat with noticeably higher probability.
Read →
Martin Ochoa
May 04, 2026
13 min read
formal-verification
zk
poseidon
lean
clean
We walk through a Lean 4 proof of correctness for a Clean model of circomlib's optimized Poseidon hash circuit at arity 1. The theorem says the modeled constraints are sound and complete with respect to the optimized Poseidon spec. After weeks of work, the only remaining `sorry` was a primality proof for the BN254 scalar field: a 254-bit number that no proof assistant can decide by trial division. Closing it requires a Pratt certificate, a recursive proof structure based on a theorem Lucas published in 1876.
Read →
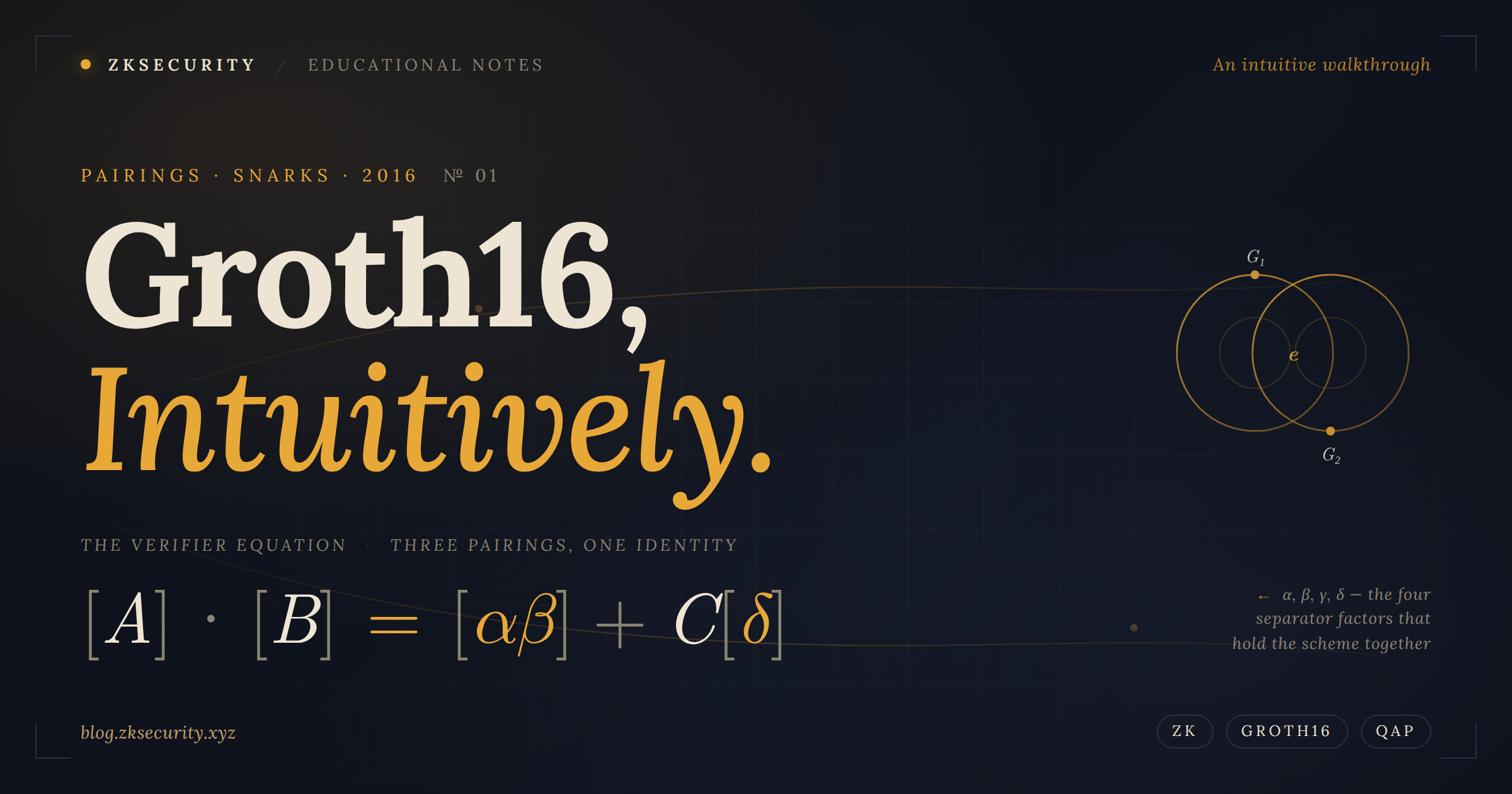
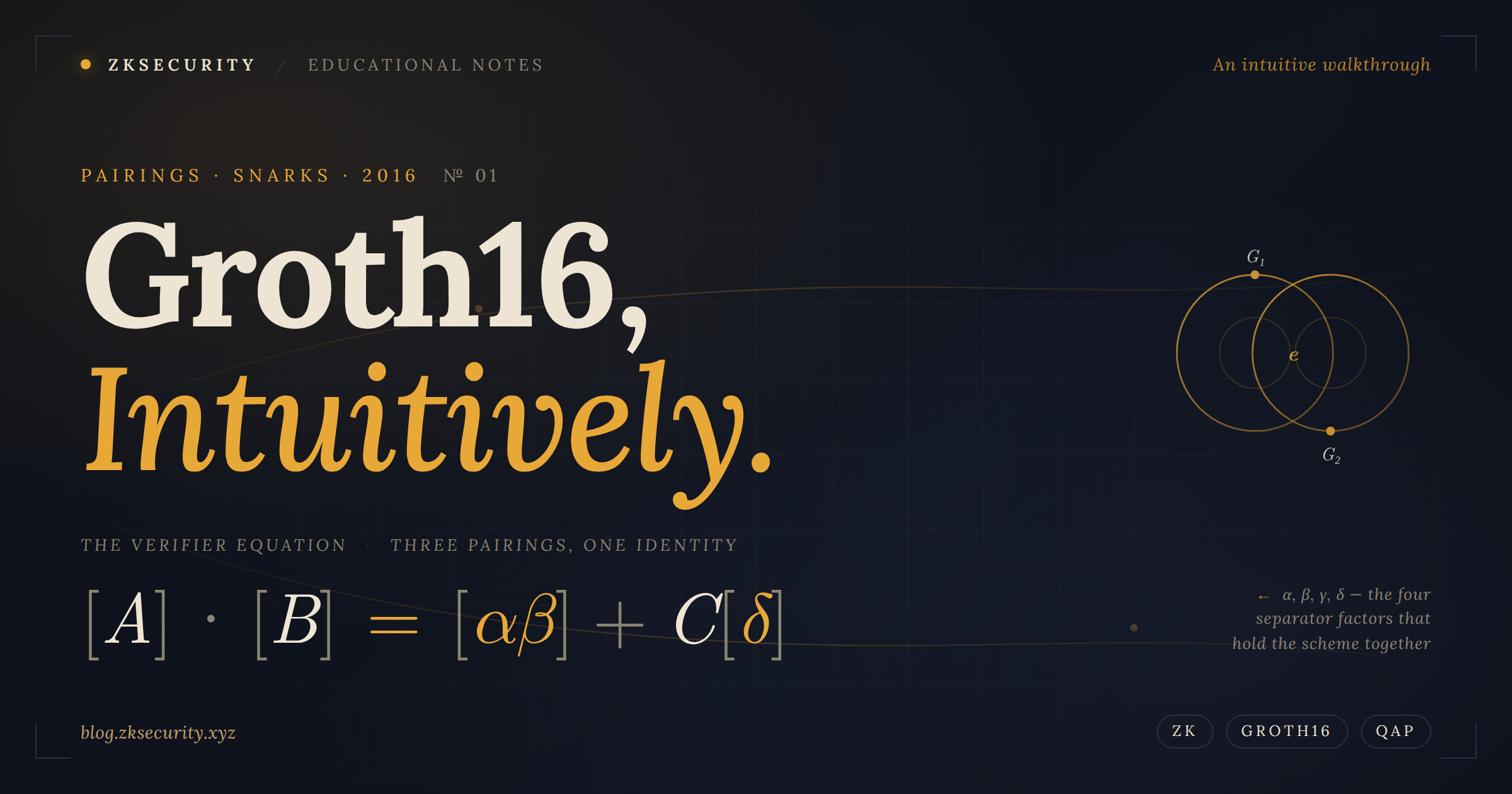
David Wong
May 01, 2026
21 min read
educative
zk
groth16
Groth16 is still the gold standard for succinct SNARKs: 128-byte proofs, constant-size verification, and a decade of real-world deployment. But despite its ubiquity, almost nobody explains *why* it works the way it does. In this post, we build Groth16 from the ground up, starting from R1CS and QAPs, then layer in pairings, trusted setup parameters, and the separator tricks (α, β, γ, δ) that make the scheme sound. By the end, you should have an intuitive grasp of every term in the final verifier equation.
Read →

Georgios Raikos
April 30, 2026
15 min read
zk
pqc
lattice
Post-quantum cryptography is making its way into production libraries, and correct implementation is far from trivial. We reviewed several LaBRADOR implementations on GitHub and found three of them broken, with soundness collapsing as far as a single bit, because of parameter choices that look perfectly reasonable in many lattice-based protocols; a power-of-2 modulus, a composite modulus, or NTT-friendly rings for efficient ring multiplication. The post goes through how each of those choices undermines the protocol's soundness argument, and why NTT-friendliness, of all things, turns out to be the wrong instinct if not handled carefully.
Read →
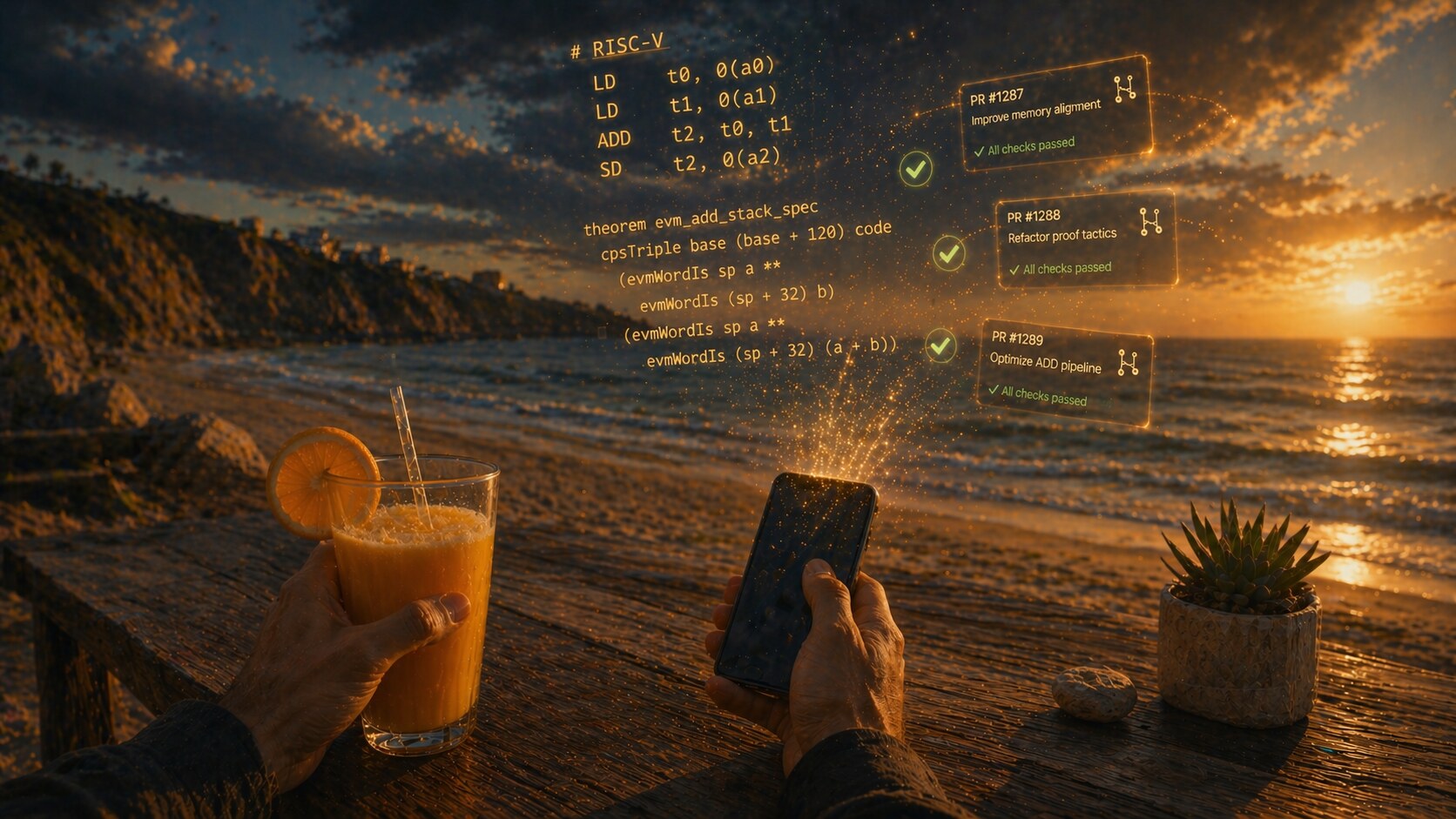
Yoichi Hirai
April 29, 2026
9 min read
zk
formal-verification
AI
lean
educative
What if the final form of software development was just watching code and proof popping up while you sip a drink? Letting AI agents write assembly directly alongside Lean proofs sidesteps the whole compiler-trust problem. With a peek at real EVM 256-bit addition code and its specification, you'll see why the assembly + Lean paradigm is final in both the historical and category theoretic sense.
Read →
Minsun Kim
April 28, 2026
13 min read
educative
sagemath
lattice
Minsun shares a high-level overview of the hard cryptography challenges he authored for KalmarCTF 2026, focusing on the broader ideas behind their design and solutions. The post reflects on how subtle randomness failures and algebraic structure can lead to deep vulnerabilities.
Read →
Marco Besier
April 27, 2026
8 min read
sum-check
algebraic reductions of knowledge
tensors
This post introduces algebraic tensor reductions as a unifying framework for understanding recursive proof protocols, using sum-check as the main motivating example. It walks through one recursive step of sum-check, showing how the prover sends a univariate summary, the verifier checks sum consistency, and the original claim is reduced to a smaller claim with one fewer variable. A small bivariate example illustrates how this “peel off one variable, check, then fold with randomness” pattern works concretely. The post sets up the rest of the series, which will introduce the tensor language needed to recover classical sum-check as an algebraic tensor reduction.
Read →
ZK/SEC
April 02, 2026
2 min read
educative
zk
bitcoin
In Session 09 of "Proof is in the Pudding," we explore the intersection of zero-knowledge proofs and Bitcoin. We break down Bitcoin's UTXO model and Script limitations, then dive deep into approaches for verifying ZK proofs on Bitcoin, from MPC-based techniques to BitVM's optimistic verification with fraud proofs. We cover timelocks, the statelessness problem and Lamport signatures for state, Taproot, simulated covenants, BitVM 3 with hashlocks and garbled circuits, cut-and-choose security, and witness encryption (BABE).
Read →